Building the Digital Infrastructure for Open and Inclusive Ecosystems
How Registries, Trust Networks, and Verifiable Credentials Can Transform Public Service Delivery
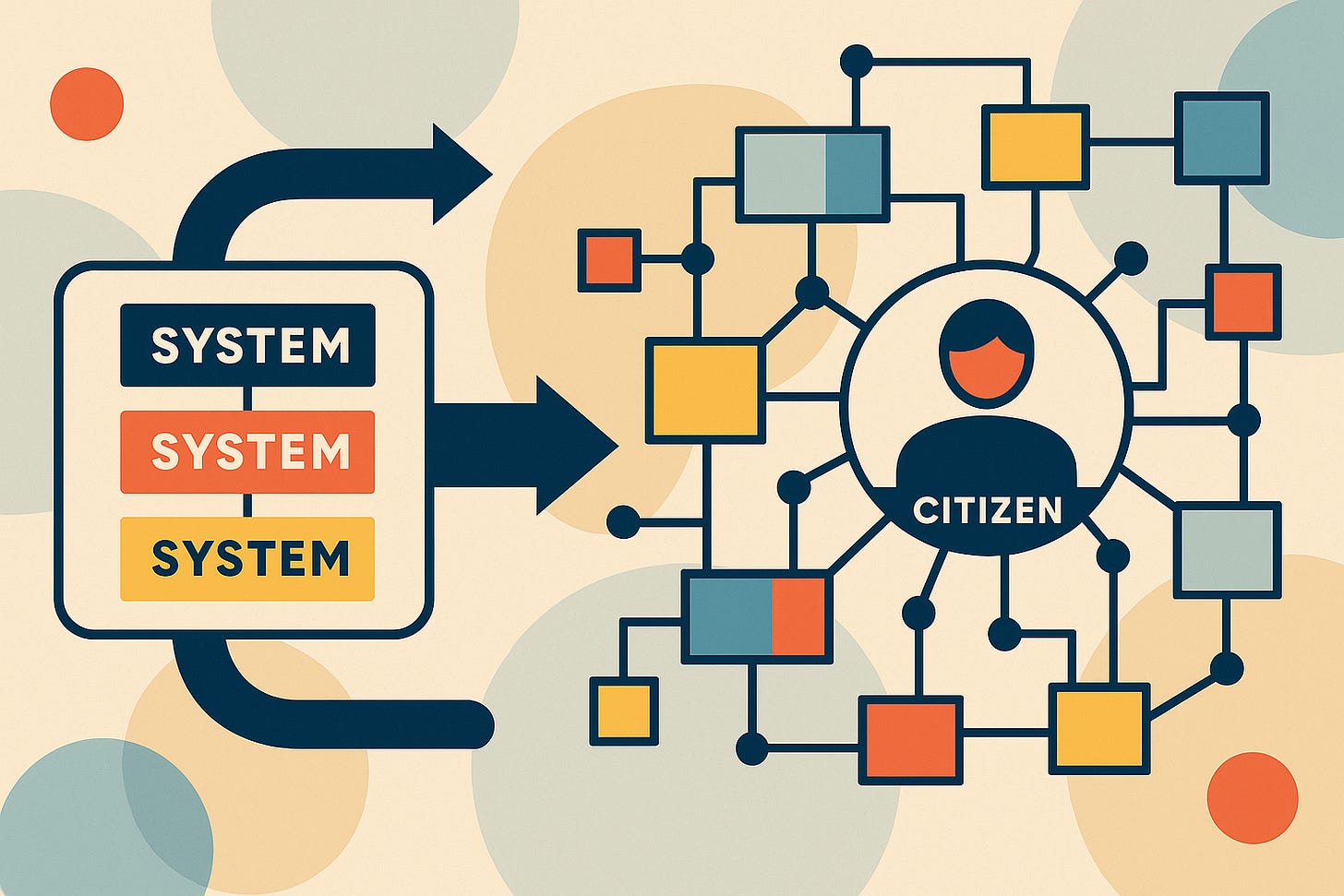
Closed and siloed institutions were once necessary. They were built during times of scarcity to deliver essential services under tight constraints. But today, these same institutions are struggling to keep up. In a world of growing populations, urbanisation, and increasing complexity, public systems face a fundamental challenge: how to scale without losing trust, flexibility, or fairness.
Nowhere is this tension more evident than in developing countries. As economies grow and demand rises, public institutions increasingly face bottlenecks in delivering healthcare, education, social protection, justice, and business services. Access is often rationed not by law, but by capacity. Citizens are denied timely services not because they lack eligibility, but because institutions lack the infrastructure to deliver at scale. They wait not because the system is unjust, but because it is overwhelmed. It is not always intent that fails, but capacity. Institutions that cannot scale cannot be just. As the saying goes, justice delayed is justice denied — but today, denial often stems not from malice, but from systemic incapacity.
To serve millions more, we must reimagine the architecture of public systems. That means moving beyond single-window portals and closed platforms. It means building an open, modular ecosystem that is capable of both scale and trust. And to do that, we can learn a great deal from a system that has already solved for scale: the Internet
Learning from the Internet
Most people experience the Internet as something seamless: you enter a web address, hit enter, and a website appears. But beneath that simplicity lies a remarkable architecture. The Internet is not a single system. It is a network of loosely coupled components — protocols, registries, identities, endpoints. What makes it powerful is that no one controls it in its entirety, yet anyone can participate. And crucially, it scales globally.
How does this work?
When you type a web address like example.com, your computer doesn’t know where that site lives. It queries a global directory called the Domain Name System (DNS), which maps domain names to IP addresses — the Internet’s version of unique identifiers. Once it gets the address, your browser connects to the server using HTTP, a universal protocol that defines how information is requested and delivered. This exchange works only because both browser and server speak the same language.
Importantly, no one entity had to approve the creation of that website. No central authority verifies every request. What enables trust and functionality is a combination of open standards and trusted registries. DNS is globally accepted, IPs are issued by distributed authorities, and HTTP is openly documented. Any browser, on any device, in any country, can speak to any server.
“The magic of the Internet lies in the invisibility of its underlying infrastructure — users don’t see the DNS queries, IP routing, or protocol handshakes. But they work reliably in the background, making scale, openness, and interoperability feel seamless.”
Modularity. Interoperability. Federated trust.
But while the Internet is open, inclusive, and scales remarkably well, it is not inherently trustworthy. Anyone can publish information, but not all information can be trusted. The same openness that makes it powerful also makes it vulnerable — to misinformation, fraud, and impersonation.
This is where public institutions have a critical role to play. They can adopt the Internet’s architecture of scale and openness, but plug in institutional trust — by creating networks of trust and publishing authoritative data. By defining who is trusted to issue what, what formats are valid, and what actions are auditable, governments can bring both credibility and accountability into the ecosystem.
This design doesn’t just solve for communication. It solves for scale with trust. And scale with trust is exactly what many public institutions lack today.
Why Scale Matters for Inclusion
In developing countries, the absence of institutional scale is often the root cause of exclusion. Not all citizens lack legal entitlements — but many are unable to exercise them because systems are not designed to handle the volume, complexity, or diversity of demand.
A student might qualify for a scholarship but struggle to prove identity, income, or eligibility. A business might meet all the conditions for a license but spend weeks navigating disconnected approvals. A pregnant mother might be entitled to benefits but abandon the process midway due to friction.
These are not failures of intent. They are failures of architecture.
When systems cannot interoperate or trust each other’s data, every department becomes a checkpoint. Every interaction becomes a fresh start. And access becomes a test of endurance.
We don’t need more portals. We need better infrastructure.
From Monoliths to Modular Ecosystems
What if public systems could work like the Internet?
What if institutions remained autonomous but participated in a shared digital network? What if services were decoupled from platforms, and information flowed through registries instead of brittle, hardwired integrations? What if citizens and businesses could carry their credentials across domains without requiring verification?
The building blocks already exist. But we need to assemble them with clarity and intent.
The Building Blocks of an Open Ecosystem
1. Directory of Participants
Just as DNS helps your browser find the right server, public systems need a directory of institutions. This directory should list which department provides which services, what APIs or portals are available, and how others can interact with them. It must be public, searchable, and regularly updated.
2. Trust Registries
The Internet works because we agree to trust certain root authorities to manage DNS and issue certificates. Similarly, public systems must answer a foundational question: who is trusted to issue what? A trust registry allows a government or consortium to declare which issuers are trusted to certify age, income, disability, education, and more. It’s a machine-readable way of saying: “We accept this credential from this issuer.”
3. Data Format Catalogues
Interoperability begins with shared meaning. Just as HTTP defines standard methods (GET, POST) and formats (HTML, JSON), public systems must publish data format catalogues. These define what an address looks like, how a license is structured, or what fields are required in a subsidy application. With shared formats, institutions don’t need to negotiate data exchange every time.
4. Verifiable Credentials and Consent
Instead of passing data behind the scenes, institutions can issue verifiable credentials directly to citizens and businesses. These credentials are digitally signed and tamper-proof. When needed, the holder presents them to another institution, which verifies them using the trust registry. Consent becomes embedded in the flow. Privacy is preserved. Reuse becomes seamless.
5. Event Streams for Observability
Transparency shouldn’t have to wait for audits. Institutions can emit non-personal event logs when credentials are issued, applications received, or services delivered. Regulators can monitor these streams to detect anomalies, enforce standards, and ensure inclusion. It becomes possible to see how the system behaves, not just what it promises.
Example 1: Business License Issuance
In a previous blog, I described the journey of an entrepreneur trying to start a business. She needs a trade license, GST registration, fire clearance, and pollution certificate. Each department demands the same documents. None talks to the other. Even so-called single windows become dead ends, pushing her back to department portals.
Now imagine the same flow in an open ecosystem.
Each department publishes what inputs it requires and what credentials it accepts. Each credential is issued as a verifiable credential and stored in the entrepreneur’s wallet. When she applies for a subsidy or a renewal, she presents her credentials. The receiving department verifies them against the trust registry. No re-entry. No fresh uploads. No gatekeeping.
If a credential is denied, an event is logged with a reason code. Regulators can detect delays, check compliance, and respond. Intermediaries can help orchestrate the journey.
This isn’t about digitisation. It’s about coordination at scale.
Example 2: Disaster Relief Disbursement
When floods hit a district, local authorities scramble to assess damage, compile beneficiary lists, and disburse emergency funds or material assistance. Currently, this process is marred by outdated formats, paper trails, fragmented systems, and repeated verifications.
Affected families must submit affidavits, ration cards, photos of damaged property, and often visit multiple offices to “prove” their eligibility. Officials manually cross-check lists, confirm identity and damage, and prepare fund release proposals. Payments are delayed by weeks or even months — when they’re needed most.
Now imagine the same response in a DPI-enabled ecosystem.
In a DPI World:
Verified Beneficiary Registry: Families are pre-enrolled in a disaster-vulnerable household registry, based on housing type, floodplain risk, and socio-economic data. This registry is updated continuously by local authorities and validated with satellite and local survey data.
Standardised Credential Formats: A damage assessment app used by local officials generates a “Flood Damage Certificate” in a verifiable credential format — digitally signed by the authorized surveyor. The certificate includes GPS-tagged photos, severity score, and timestamp, based on a published damage assessment data schema.
Rule-based Eligibility: Relief rules are codified in a machine-readable format: e.g., “If household is in flood zone and has certified damage above threshold, release ₹5,000 compensation”. These rules are published along with credential formats in the DPI catalogue.
Automated Verification & Payment Instruction: Once the damage certificate is uploaded by the field officer and matched with the beneficiary registry, the payment instruction is automatically generated and passed to the finance system. No need for separate summaries, proposals, or approvals.
Real-Time Transparency: Dashboards show how many households have been assessed, certified, and paid — disaggregated by district, gender, caste, and income level — without compromising personal data. Regulators see compliance issues or bottlenecks via event streams.
Improved Service Delivery: Payments reach affected families within 48 hours, reducing distress and preventing exploitative borrowing. NGOs and relief workers use real-time data to focus support efforts. Funders (national or international) can track how their grants are being used, in near real-time.
Consent-Driven Coordination: If the same families later seek rebuilding support or a loan, they can present their damage certificate from their wallet to other departments or banks — no re-submission, no re-verification.
Why This Matters
This example showcases trust at scale:
Trusted credentials issued by field officers,
Trusted registries maintained by local governments,
Trusted verification rules defined by the central relief agency.
It replaces bureaucratic back-and-forth with coordinated, standards-driven flows. Importantly, no one system has to control everything — local flexibility is preserved while ensuring national-level observability and fiscal discipline.
The Role of the Government
The Internet solved for scale. But it didn’t solve for trust. That’s where public institutions must lead.
Governments have a unique role to play in publishing:
Trusted registries: Who is authorized to issue or verify what
Data standards: What formats are accepted and understood
Rules of participation: What is allowed, expected, and auditable
They must act as anchors of trust in an open system. Not by owning all the infrastructure, but by shaping the conditions under which it thrives.
This is not just a technology agenda. It is a governance imperative. And it starts with simple, visible steps that institutional leaders can take today:
Publish a trust registry: Identify and publicly declare which institutions are trusted to issue or verify specific credentials such as income, education, address, or age.
Declare accepted data formats: Make it clear what data structures and formats will be accepted for each service or credential.
List available services and APIs: Let others discover and connect to your services by publishing the list of digital services, their inputs, and endpoints.
Issue verifiable credentials: Begin issuing key certificates and approvals as digitally signed, reusable credentials.
Emit non-personal service events: Log key actions (like issuance or rejection) as auditable events to build transparency and enable observability.
These actions do not require perfect systems. They require intent and leadership. They create the foundation for modular, scalable, and inclusive ecosystems. The shift begins not with transformation at scale, but with trust made visible.
Conclusion: Scale with Trust
Public systems are at an inflection point. Yes, we must continue improving portals and apps — but that alone won’t solve the deeper problem. The real challenge is not better interfaces, but better integration. Today’s systems are siloed, each optimized for internal workflows, but unable to work together.
To move forward, we need to zoom out from isolated systems to the larger ecosystem — where information flows seamlessly across departments, jurisdictions, and service providers. That shift begins when we step out of the institutional lens that asks, “How can I improve my system?” and adopt a citizen-centric lens that asks, “How can people get what they need — faster, with less friction, and more transparency?”
We can continue building bigger portals, or we can wire up better networks. The future demands systems that are open enough to adapt, modular enough to grow, and trusted enough to be relied upon.
The Internet has shown us how to scale. Now we must apply its lessons with care. Because in governance, scale without trust leads to control, and trust without scale leads to exclusion.
We need both. And we need them now.